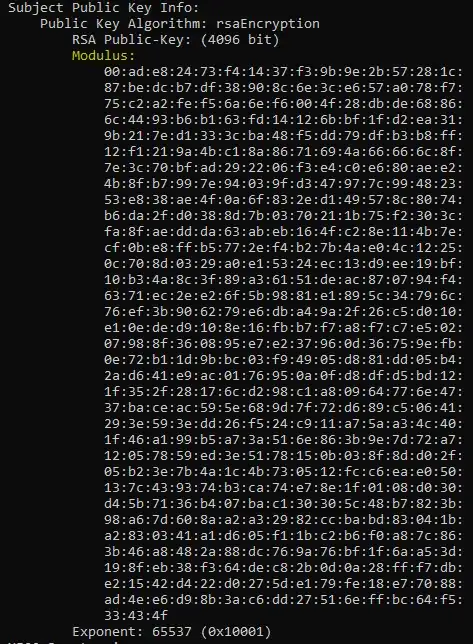
I've exported the root CA cert (ISRG Root X1) used by StackOverflow's digital certificate, as a DER encoded binary X.509 (.cer) file and used openssl in cmd to find out the modulus/exponent:
openssl.exe x509 -in C:\Cert.cer -inform der -text
I then did the same thing for the next certificate in the chain which is called R3, to get the signature:
Signature for R3:
I've copied these into C# as byte arrays and am using the following code to decrypt the signature:
using System.Security.Cryptography;
namespace RsaDecryptor
{
class Program
{
static void Main(string[] args)
{
byte[] decryptedData;
using (RSACryptoServiceProvider rsa = new RSACryptoServiceProvider())
{
var bytesRead = 0;
// From ISRG root CA:
var modulus = new byte[] { 0xad, 0xe8, 0x24, 0x73, 0xf4, 0x14, 0x37, 0xf3, 0x9b, 0x9e, 0x2b, 0x57, 0x28, 0x1c,
0x87, 0xbe, 0xdc, 0xb7, 0xdf, 0x38, 0x90, 0x8c, 0x6e, 0x3c, 0xe6, 0x57, 0xa0, 0x78, 0xf7, 0x75, 0xc2, 0xa2,
0xfe, 0xf5, 0x6a, 0x6e, 0xf6, 0x00, 0x4f, 0x28, 0xdb, 0xde, 0x68, 0x86, 0x6c, 0x44, 0x93, 0xb6, 0xb1, 0x63,
0xfd, 0x14, 0x12, 0x6b, 0xbf, 0x1f, 0xd2, 0xea, 0x31, 0x9b, 0x21, 0x7e, 0xd1, 0x33, 0x3c, 0xba, 0x48, 0xf5,
0xdd, 0x79, 0xdf, 0xb3, 0xb8, 0xff, 0x12, 0xf1, 0x21, 0x9a, 0x4b, 0xc1, 0x8a, 0x86, 0x71, 0x69, 0x4a, 0x66,
0x66, 0x6c, 0x8f, 0x7e, 0x3c, 0x70, 0xbf, 0xad, 0x29, 0x22, 0x06, 0xf3, 0xe4, 0xc0, 0xe6, 0x80, 0xae, 0xe2,
0x4b, 0x8f, 0xb7, 0x99, 0x7e, 0x94, 0x03, 0x9f, 0xd3, 0x47, 0x97, 0x7c, 0x99, 0x48, 0x23, 0x53, 0xe8, 0x38,
0xae, 0x4f, 0x0a, 0x6f, 0x83, 0x2e, 0xd1, 0x49, 0x57, 0x8c, 0x80, 0x74, 0xb6, 0xda, 0x2f, 0xd0, 0x38, 0x8d,
0x7b, 0x03, 0x70, 0x21, 0x1b, 0x75, 0xf2, 0x30, 0x3c, 0xfa, 0x8f, 0xae, 0xdd, 0xda, 0x63, 0xab, 0xeb, 0x16,
0x4f, 0xc2, 0x8e, 0x11, 0x4b, 0x7e, 0xcf, 0x0b, 0xe8, 0xff, 0xb5, 0x77, 0x2e, 0xf4, 0xb2, 0x7b, 0x4a, 0xe0,
0x4c, 0x12, 0x25, 0x0c, 0x70, 0x8d, 0x03, 0x29, 0xa0, 0xe1, 0x53, 0x24, 0xec, 0x13, 0xd9, 0xee, 0x19, 0xbf,
0x10, 0xb3, 0x4a, 0x8c, 0x3f, 0x89, 0xa3, 0x61, 0x51, 0xde, 0xac, 0x87, 0x07, 0x94, 0xf4, 0x63, 0x71, 0xec,
0x2e, 0xe2, 0x6f, 0x5b, 0x98, 0x81, 0xe1, 0x89, 0x5c, 0x34, 0x79, 0x6c, 0x76, 0xef, 0x3b, 0x90, 0x62, 0x79,
0xe6, 0xdb, 0xa4, 0x9a, 0x2f, 0x26, 0xc5, 0xd0, 0x10, 0xe1, 0x0e, 0xde, 0xd9, 0x10, 0x8e, 0x16, 0xfb, 0xb7,
0xf7, 0xa8, 0xf7, 0xc7, 0xe5, 0x02, 0x07, 0x98, 0x8f, 0x36, 0x08, 0x95, 0xe7, 0xe2, 0x37, 0x96, 0x0d, 0x36,
0x75, 0x9e, 0xfb, 0x0e, 0x72, 0xb1, 0x1d, 0x9b, 0xbc, 0x03, 0xf9, 0x49, 0x05, 0xd8, 0x81, 0xdd, 0x05, 0xb4,
0x2a, 0xd6, 0x41, 0xe9, 0xac, 0x01, 0x76, 0x95, 0x0a, 0x0f, 0xd8, 0xdf, 0xd5, 0xbd, 0x12, 0x1f, 0x35, 0x2f,
0x28, 0x17, 0x6c, 0xd2, 0x98, 0xc1, 0xa8, 0x09, 0x64, 0x77, 0x6e, 0x47, 0x37, 0xba, 0xce, 0xac, 0x59, 0x5e,
0x68, 0x9d, 0x7f, 0x72, 0xd6, 0x89, 0xc5, 0x06, 0x41, 0x29, 0x3e, 0x59, 0x3e, 0xdd, 0x26, 0xf5, 0x24, 0xc9,
0x11, 0xa7, 0x5a, 0xa3, 0x4c, 0x40, 0x1f, 0x46, 0xa1, 0x99, 0xb5, 0xa7, 0x3a, 0x51, 0x6e, 0x86, 0x3b, 0x9e,
0x7d, 0x72, 0xa7, 0x12, 0x05, 0x78, 0x59, 0xed, 0x3e, 0x51, 0x78, 0x15, 0x0b, 0x03, 0x8f, 0x8d, 0xd0, 0x2f,
0x05, 0xb2, 0x3e, 0x7b, 0x4a, 0x1c, 0x4b, 0x73, 0x05, 0x12, 0xfc, 0xc6, 0xea, 0xe0, 0x50, 0x13, 0x7c, 0x43,
0x93, 0x74, 0xb3, 0xca, 0x74, 0xe7, 0x8e, 0x1f, 0x01, 0x08, 0xd0, 0x30, 0xd4, 0x5b, 0x71, 0x36, 0xb4, 0x07,
0xba, 0xc1, 0x30, 0x30, 0x5c, 0x48, 0xb7, 0x82, 0x3b, 0x98, 0xa6, 0x7d, 0x60, 0x8a, 0xa2, 0xa3, 0x29, 0x82,
0xcc, 0xba, 0xbd, 0x83, 0x04, 0x1b, 0xa2, 0x83, 0x03, 0x41, 0xa1, 0xd6, 0x05, 0xf1, 0x1b, 0xc2, 0xb6, 0xf0,
0xa8, 0x7c, 0x86, 0x3b, 0x46, 0xa8, 0x48, 0x2a, 0x88, 0xdc, 0x76, 0x9a, 0x76, 0xbf, 0x1f, 0x6a, 0xa5, 0x3d,
0x19, 0x8f, 0xeb, 0x38, 0xf3, 0x64, 0xde, 0xc8, 0x2b, 0x0d, 0x0a, 0x28, 0xff, 0xf7, 0xdb, 0xe2, 0x15, 0x42,
0xd4, 0x22, 0xd0, 0x27, 0x5d, 0xe1, 0x79, 0xfe, 0x18, 0xe7, 0x70, 0x88, 0xad, 0x4e, 0xe6, 0xd9, 0x8b, 0x3a,
0xc6, 0xdd, 0x27, 0x51, 0x6e, 0xff, 0xbc, 0x64, 0xf5, 0x33, 0x43, 0x4f };
// From R3 intermediate CA:
var signature = new byte[] { 0x85, 0xca, 0x4e, 0x47, 0x3e, 0xa3, 0xf7, 0x85, 0x44, 0x85, 0xbc, 0xd5, 0x67, 0x78,
0xb2, 0x98, 0x63, 0xad, 0x75, 0x4d, 0x1e, 0x96, 0x3d, 0x33, 0x65, 0x72, 0x54, 0x2d, 0x81, 0xa0, 0xea, 0xc3,
0xed, 0xf8, 0x20, 0xbf, 0x5f, 0xcc, 0xb7, 0x70, 0x00, 0xb7, 0x6e, 0x3b, 0xf6, 0x5e, 0x94, 0xde, 0xe4, 0x20,
0x9f, 0xa6, 0xef, 0x8b, 0xb2, 0x03, 0xe7, 0xa2, 0xb5, 0x16, 0x3c, 0x91, 0xce, 0xb4, 0xed, 0x39, 0x02, 0xe7,
0x7c, 0x25, 0x8a, 0x47, 0xe6, 0x65, 0x6e, 0x3f, 0x46, 0xf4, 0xd9, 0xf0, 0xce, 0x94, 0x2b, 0xee, 0x54, 0xce,
0x12, 0xbc, 0x8c, 0x27, 0x4b, 0xb8, 0xc1, 0x98, 0x2f, 0xa2, 0xaf, 0xcd, 0x71, 0x91, 0x4a, 0x08, 0xb7, 0xc8,
0xb8, 0x23, 0x7b, 0x04, 0x2d, 0x08, 0xf9, 0x08, 0x57, 0x3e, 0x83, 0xd9, 0x04, 0x33, 0x0a, 0x47, 0x21, 0x78,
0x09, 0x82, 0x27, 0xc3, 0x2a, 0xc8, 0x9b, 0xb9, 0xce, 0x5c, 0xf2, 0x64, 0xc8, 0xc0, 0xbe, 0x79, 0xc0, 0x4f,
0x8e, 0x6d, 0x44, 0x0c, 0x5e, 0x92, 0xbb, 0x2e, 0xf7, 0x8b, 0x10, 0xe1, 0xe8, 0x1d, 0x44, 0x29, 0xdb, 0x59,
0x20, 0xed, 0x63, 0xb9, 0x21, 0xf8, 0x12, 0x26, 0x94, 0x93, 0x57, 0xa0, 0x1d, 0x65, 0x04, 0xc1, 0x0a, 0x22,
0xae, 0x10, 0x0d, 0x43, 0x97, 0xa1, 0x18, 0x1f, 0x7e, 0xe0, 0xe0, 0x86, 0x37, 0xb5, 0x5a, 0xb1, 0xbd, 0x30,
0xbf, 0x87, 0x6e, 0x2b, 0x2a, 0xff, 0x21, 0x4e, 0x1b, 0x05, 0xc3, 0xf5, 0x18, 0x97, 0xf0, 0x5e, 0xac, 0xc3,
0xa5, 0xb8, 0x6a, 0xf0, 0x2e, 0xbc, 0x3b, 0x33, 0xb9, 0xee, 0x4b, 0xde, 0xcc, 0xfc, 0xe4, 0xaf, 0x84, 0x0b,
0x86, 0x3f, 0xc0, 0x55, 0x43, 0x36, 0xf6, 0x68, 0xe1, 0x36, 0x17, 0x6a, 0x8e, 0x99, 0xd1, 0xff, 0xa5, 0x40,
0xa7, 0x34, 0xb7, 0xc0, 0xd0, 0x63, 0x39, 0x35, 0x39, 0x75, 0x6e, 0xf2, 0xba, 0x76, 0xc8, 0x93, 0x02, 0xe9,
0xa9, 0x4b, 0x6c, 0x17, 0xce, 0x0c, 0x02, 0xd9, 0xbd, 0x81, 0xfb, 0x9f, 0xb7, 0x68, 0xd4, 0x06, 0x65, 0xb3,
0x82, 0x3d, 0x77, 0x53, 0xf8, 0x8e, 0x79, 0x03, 0xad, 0x0a, 0x31, 0x07, 0x75, 0x2a, 0x43, 0xd8, 0x55, 0x97,
0x72, 0xc4, 0x29, 0x0e, 0xf7, 0xc4, 0x5d, 0x4e, 0xc8, 0xae, 0x46, 0x84, 0x30, 0xd7, 0xf2, 0x85, 0x5f, 0x18,
0xa1, 0x79, 0xbb, 0xe7, 0x5e, 0x70, 0x8b, 0x07, 0xe1, 0x86, 0x93, 0xc3, 0xb9, 0x8f, 0xdc, 0x61, 0x71, 0x25,
0x2a, 0xaf, 0xdf, 0xed, 0x25, 0x50, 0x52, 0x68, 0x8b, 0x92, 0xdc, 0xe5, 0xd6, 0xb5, 0xe3, 0xda, 0x7d, 0xd0,
0x87, 0x6c, 0x84, 0x21, 0x31, 0xae, 0x82, 0xf5, 0xfb, 0xb9, 0xab, 0xc8, 0x89, 0x17, 0x3d, 0xe1, 0x4c, 0xe5,
0x38, 0x0e, 0xf6, 0xbd, 0x2b, 0xbd, 0x96, 0x81, 0x14, 0xeb, 0xd5, 0xdb, 0x3d, 0x20, 0xa7, 0x7e, 0x59, 0xd3,
0xe2, 0xf8, 0x58, 0xf9, 0x5b, 0xb8, 0x48, 0xcd, 0xfe, 0x5c, 0x4f, 0x16, 0x29, 0xfe, 0x1e, 0x55, 0x23, 0xaf,
0xc8, 0x11, 0xb0, 0x8d, 0xea, 0x7c, 0x93, 0x90, 0x17, 0x2f, 0xfd, 0xac, 0xa2, 0x09, 0x47, 0x46, 0x3f, 0xf0,
0xe9, 0xb0, 0xb7, 0xff, 0x28, 0x4d, 0x68, 0x32, 0xd6, 0x67, 0x5e, 0x1e, 0x69, 0xa3, 0x93, 0xb8, 0xf5, 0x9d,
0x8b, 0x2f, 0x0b, 0xd2, 0x52, 0x43, 0xa6, 0x6f, 0x32, 0x57, 0x65, 0x4d, 0x32, 0x81, 0xdf, 0x38, 0x53, 0x85,
0x5d, 0x7e, 0x5d, 0x66, 0x29, 0xea, 0xb8, 0xdd, 0xe4, 0x95, 0xb5, 0xcd, 0xb5, 0x56, 0x12, 0x42, 0xcd, 0xc4,
0x4e, 0xc6, 0x25, 0x38, 0x44, 0x50, 0x6d, 0xec, 0xce, 0x00, 0x55, 0x18, 0xfe, 0xe9, 0x49, 0x64, 0xd4, 0x4e,
0xca, 0x97, 0x9c, 0xb4, 0x5b, 0xc0, 0x73, 0xa8, 0xab, 0xb8, 0x47, 0xc2 };
// The next line results in:
// AsnContentException: The encoded length exceeds the maximum supported by this library (Int32.MaxValue).
rsa.ImportRSAPublicKey(modulus, out bytesRead);
//var rsaParams = new RSAParameters();
//rsaParams.Modulus = modulus;
//rsaParams.Exponent = new byte[] { 0x01, 0x00, 0x01 };
//rsa.ImportParameters(rsaParams);
// If the 4 lines above are used instead, the following throws:
// System.Security.Cryptography.CryptographicException: 'Cryptography_OAEPDecoding'
// if fOAEP == true.
// if fOAEP == false then it throws:
// Internal.Cryptography.CryptoThrowHelper.WindowsCryptographicException: 'Key does not exist.'
var fOAEP = false;
decryptedData = rsa.Decrypt(signature, fOAEP);
}
}
}
}
rsa.ImportRSAPublicKey(modulus, out bytesRead); is failing with:
System.Security.Cryptography.CryptographicException: 'ASN1 corrupted data.'
AsnContentException: The encoded length exceeds the maximum supported by this library (Int32.MaxValue).
From the comments in the above code, you can see I'm trying another method, however this fails as well.
Is this the correct way to manually decrypt a signature using RSA?
Do I need to specify the exponent somewhere? Or is it assumed to be 65537?